- Why Panzura
- Products
- HYBRID CLOUD FILE PLATFORM
 Panzura CloudFSConsolidate file data, boost resilience and increase productivity with immediate global data delivery
Panzura CloudFSConsolidate file data, boost resilience and increase productivity with immediate global data delivery
 Panzura EdgeExtend secure, performant file access to remote and authorized external users at the edge
Panzura EdgeExtend secure, performant file access to remote and authorized external users at the edge
 Panzura Data ServicesGet complete visibility, always-on governance, and real-time global data search and retrieval
Panzura Data ServicesGet complete visibility, always-on governance, and real-time global data search and retrieval
 Panzura Detect and RescueAutomatically detect suspicious file activity in near real time and stop ransomware in its tracks
Panzura Detect and RescueAutomatically detect suspicious file activity in near real time and stop ransomware in its tracks
- DATA SERVICES PLATFORM
 Panzura SymphonyAccess comprehensive data visibility and operations under a single pane of glass.
Panzura SymphonyAccess comprehensive data visibility and operations under a single pane of glass.
-
Discover how to dramatically improve file data resilience and productivity while simplifying operations with our powerful hybrid cloud file and data services platforms.
- Solutions
- USE CASES
- NAS ConsolidationEliminate data silos and endless storage refreshes.

- Global File CollaborationForget delays and version conflicts across multiple sites.

- Disaster RecoveryGain resilience with data that bends but doesn’t break.

- Governance & ComplianceReduce inefficiencies, streamline operations, and prevent costly mistakes.

- Metadata Harvesting

- Data MigrationAccelerate large-scale data migrations with metadata awareness.

- Zero Trust Data BrokerOptimize LLM training and performance in a zero trust environment.

- INDUSTRIES
- Architecture, Engineering & ConstructionImproving time-to-value by securing data & enhancing cross-site collaboration

- Banking, Financial Services & InsuranceDelivering financial value by driving digital transformation

- Healthcare & Life SciencesProtecting patient data, improving outcomes & powering research

- ManufacturingStreamlining workflows & improving efficiency to accelerate time to market

- Media & EntertainmentPowering secure global collaboration & reducing exponential data growth

- Public SectorProviding military-grade security & enabling advanced data compliance

- Resources
- Support
- About
- ABOUT PANZURA
- Our CompanyWe charted a new path to the top — and it’s a hell of a story!

- Leadership TeamMeet mavericks, motivators & masterminds who drive our success.

- CareersWe’re looking for the best & brightest. If that’s you, let us know.

- Press RoomKeep up with our latest news, insights & company updates.

Protecting Your Data Has Never Been More Crucial
That’s why we’re here to remind you to back up your data and ensure your security protections can stand up to new threats.
Ransomware Unlocked
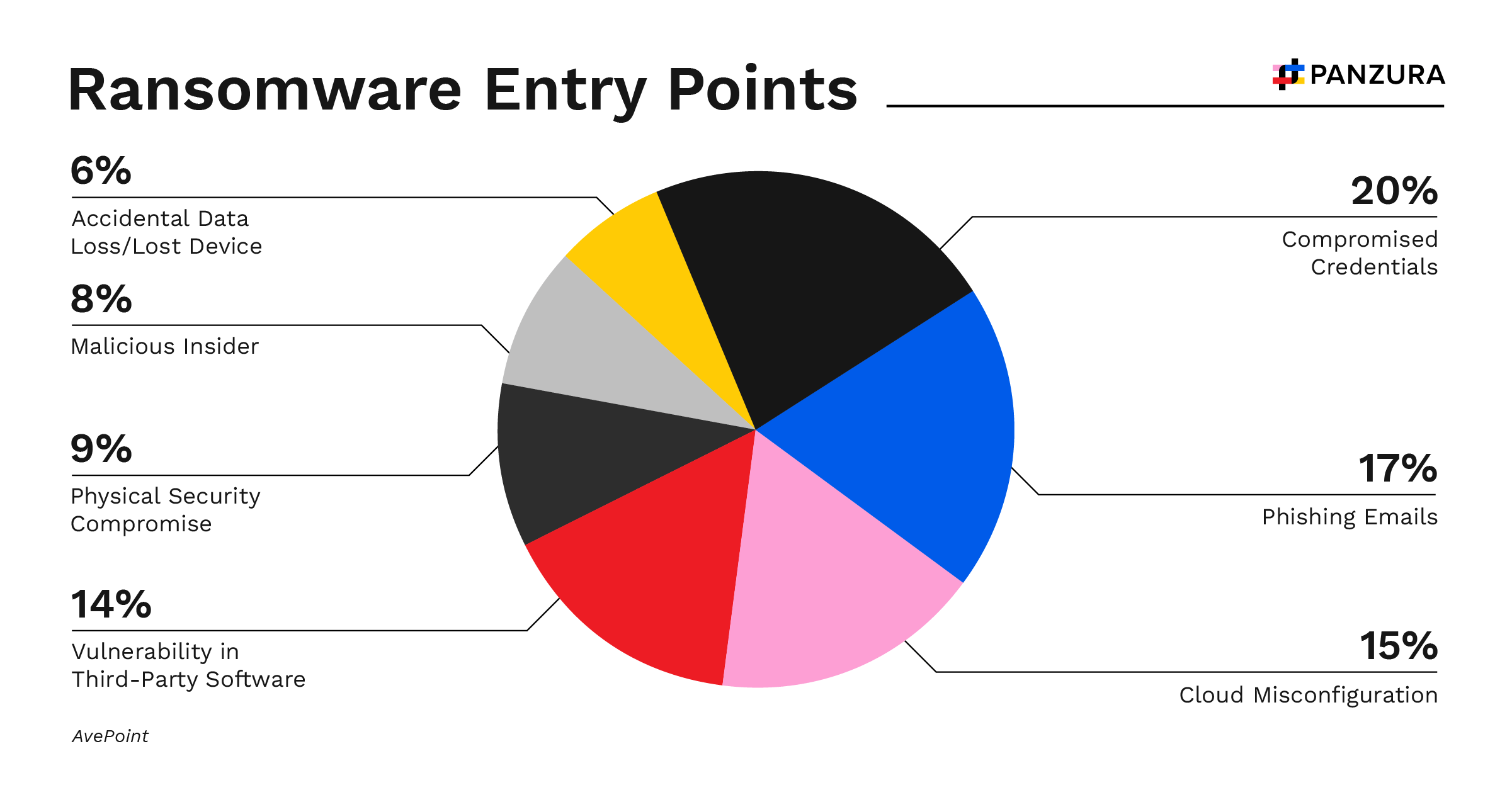
The persistence, pervasiveness, and documented success of ransomware attacks make it essential that critical business data is immutable to threats. Read on to learn about the latest ransomware trends powering the shift from prevention tactics to a data-resilient approach.
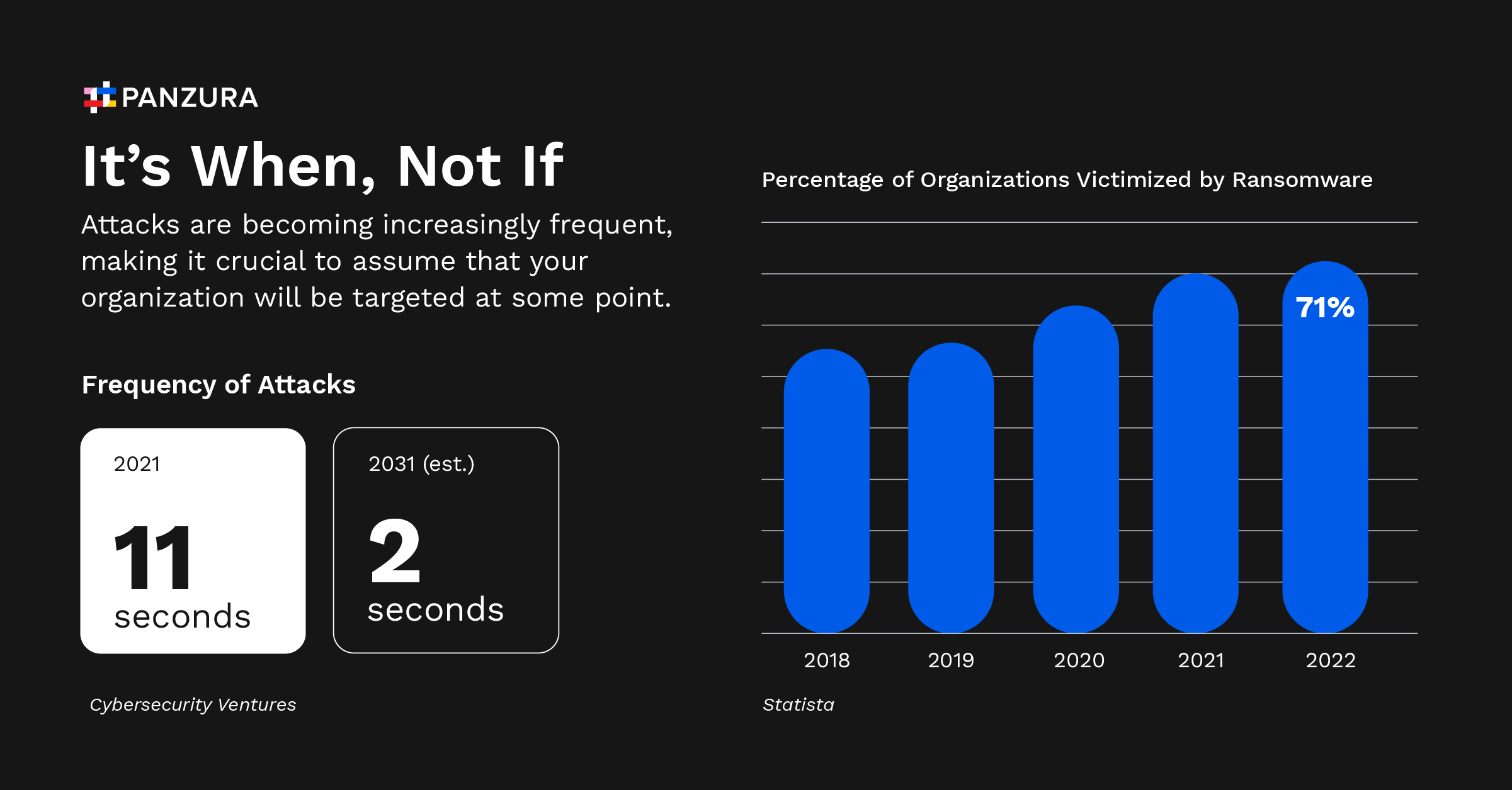
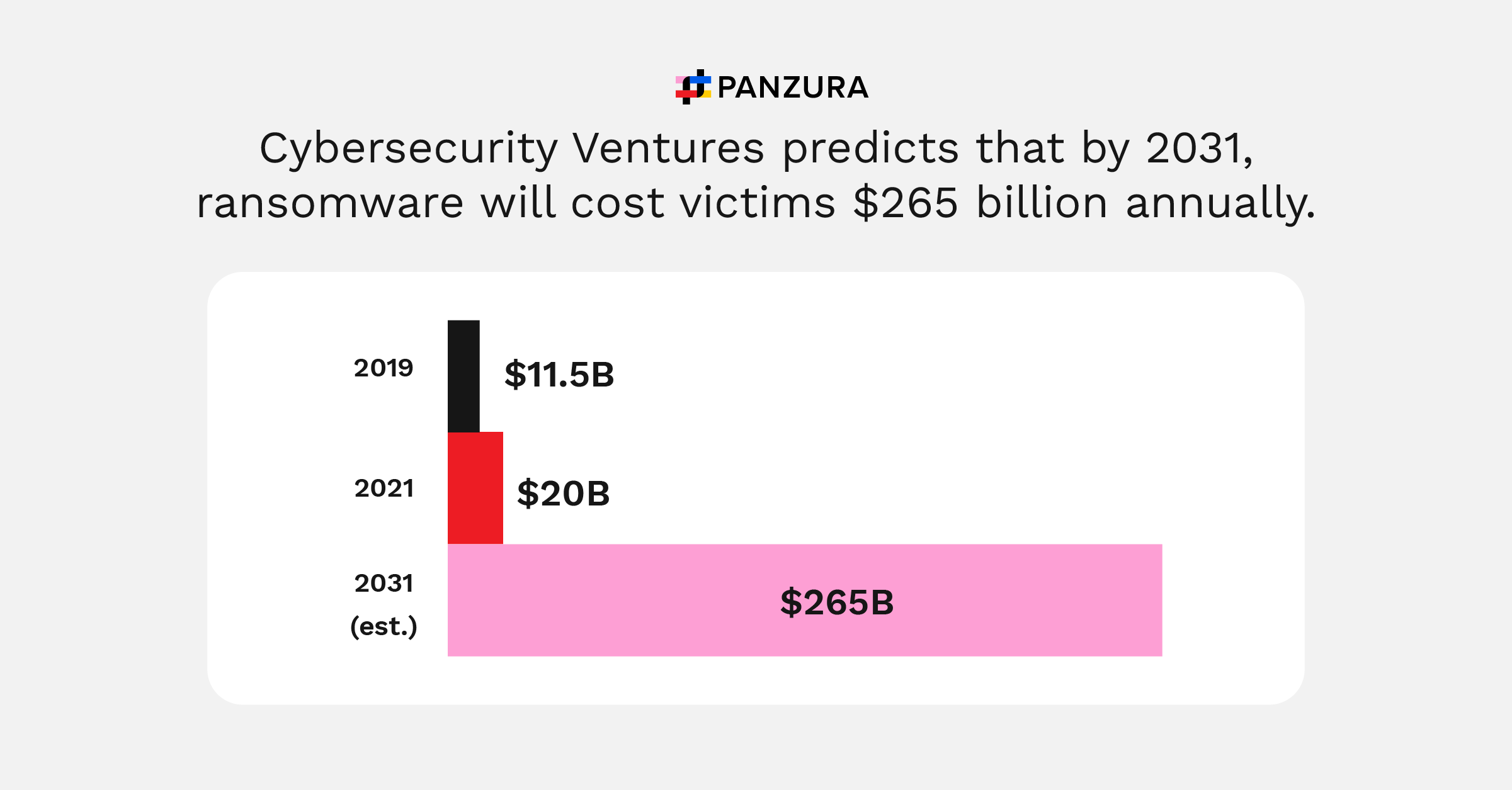
Unprotected data can cost your company a pretty penny, with the average cost of data breaches, cyber threats, and ransomware attacks projected to rise dramatically in the coming years.
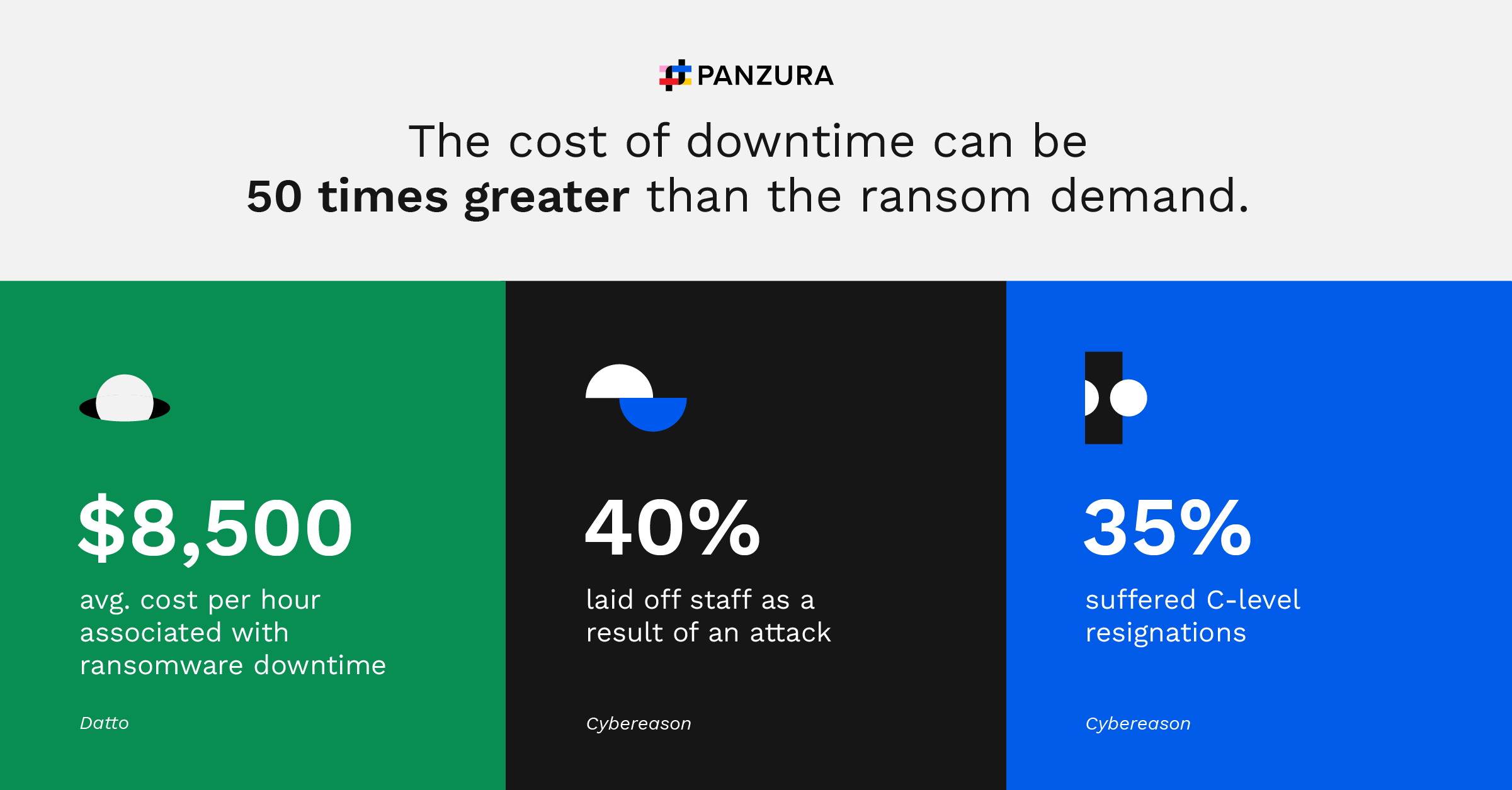
And, everyone knows that time is money. The longer your company is down, the more costly the ransomware attack becomes.
Ransomware attacks can happen quickly, with no warning. If your data is left unprotected, ransomware can strike before you know what happened.
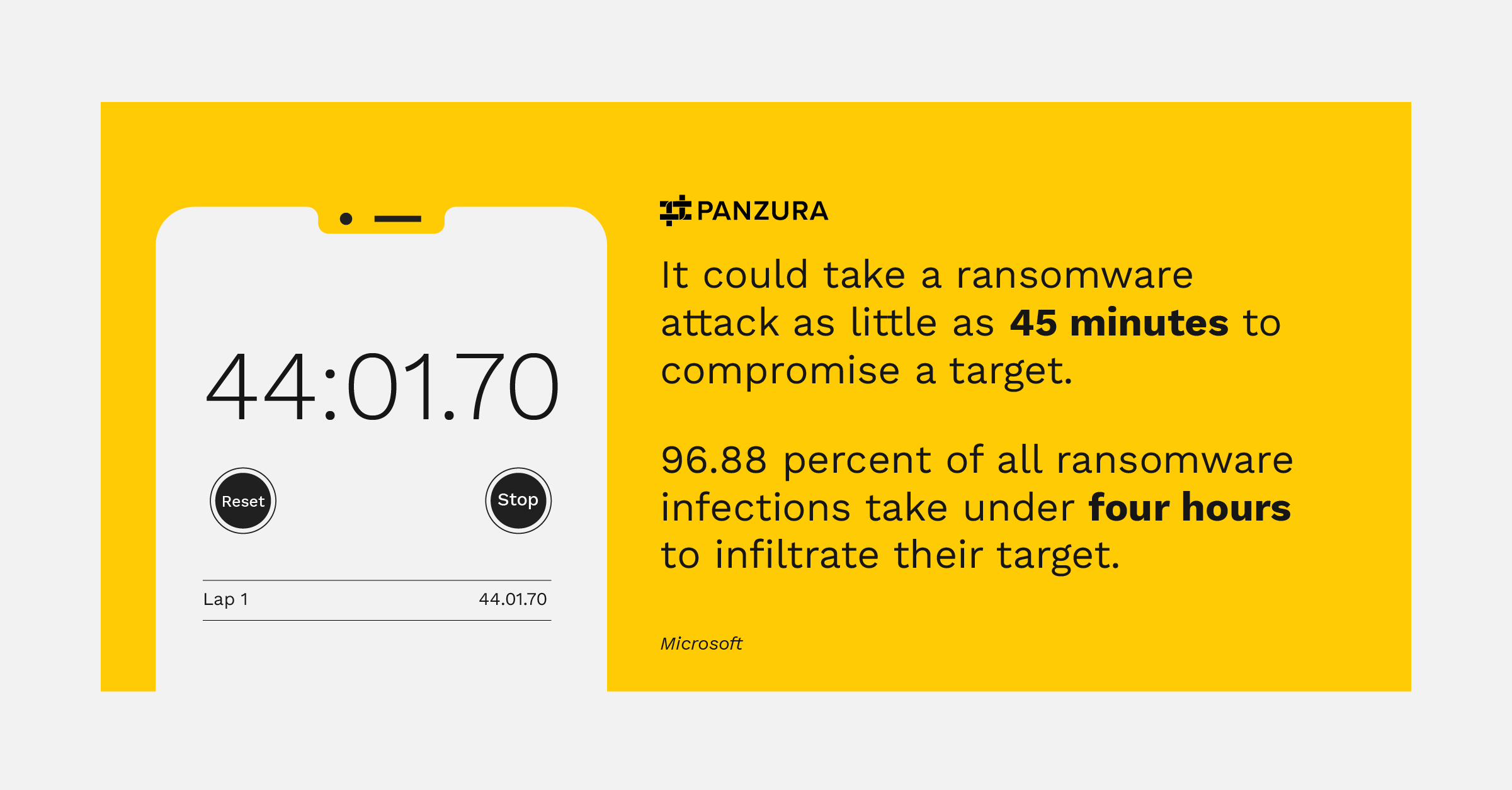
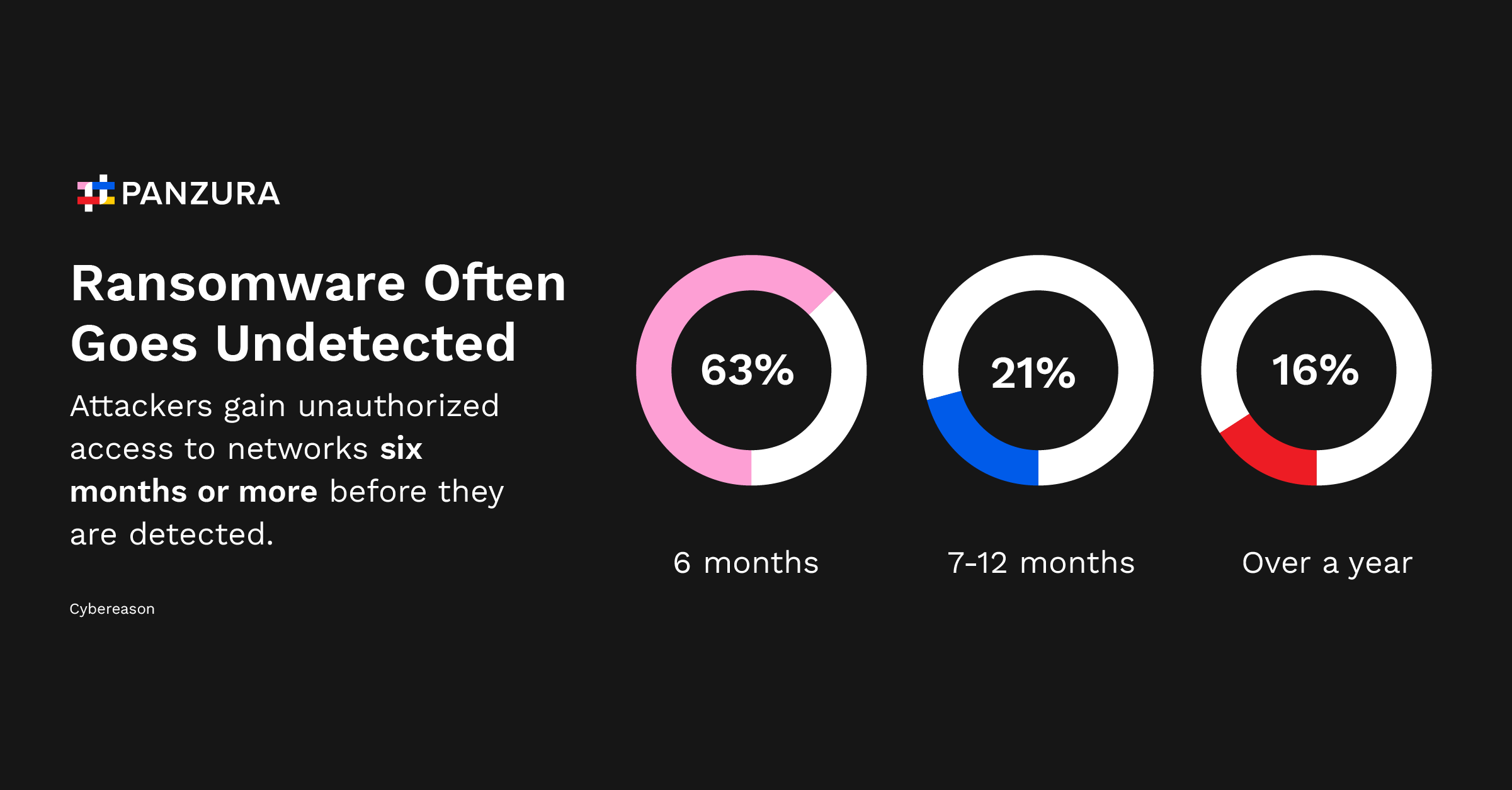
Without a proactive defense in place, your data could be compromised by ransomware and you wouldn’t know it until it’s too late.
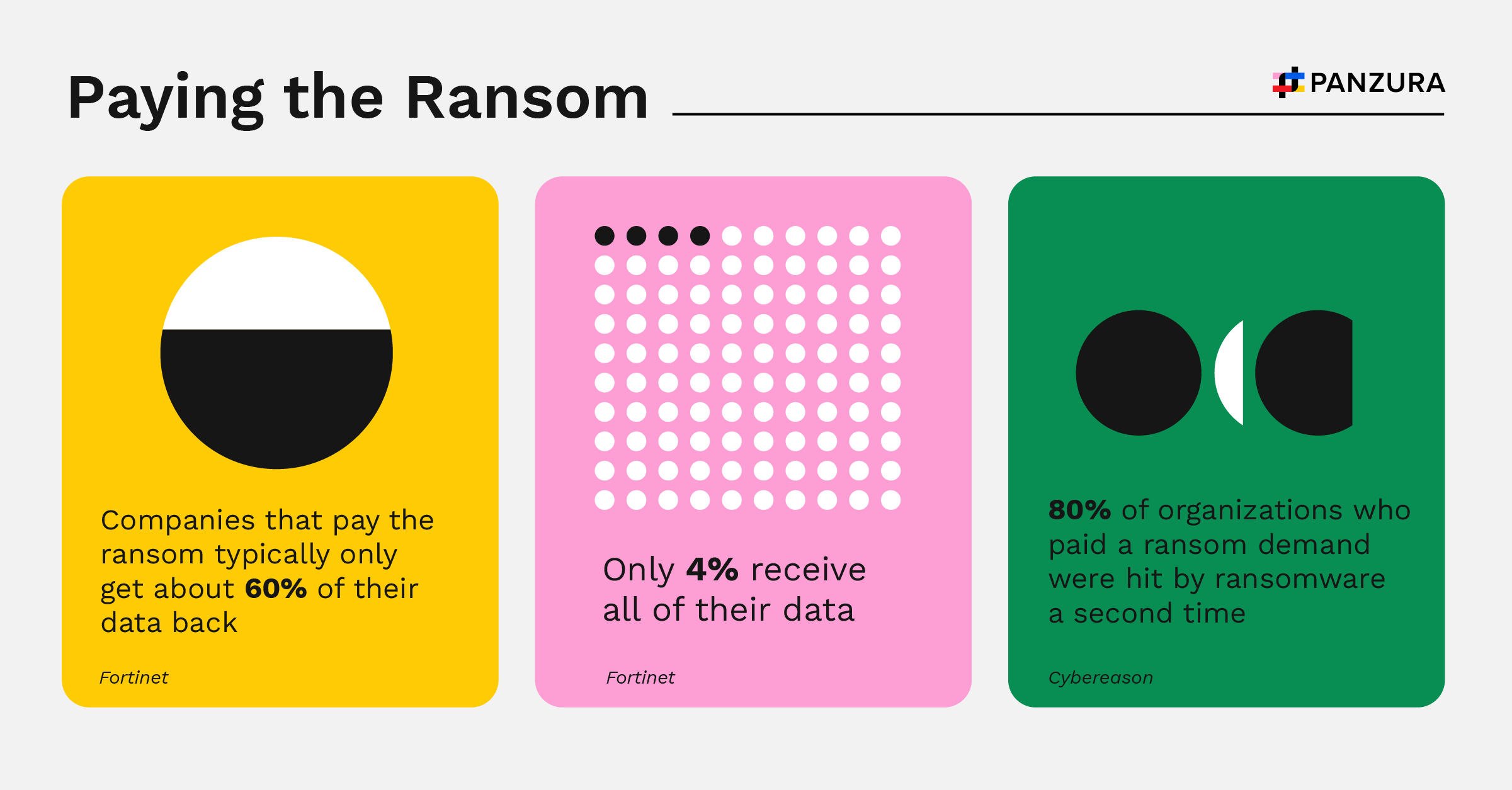
When trying to lessen the damage of a ransomware attack, don’t expect the attackers to go easy on you. And don’t expect to get all of your data back either.
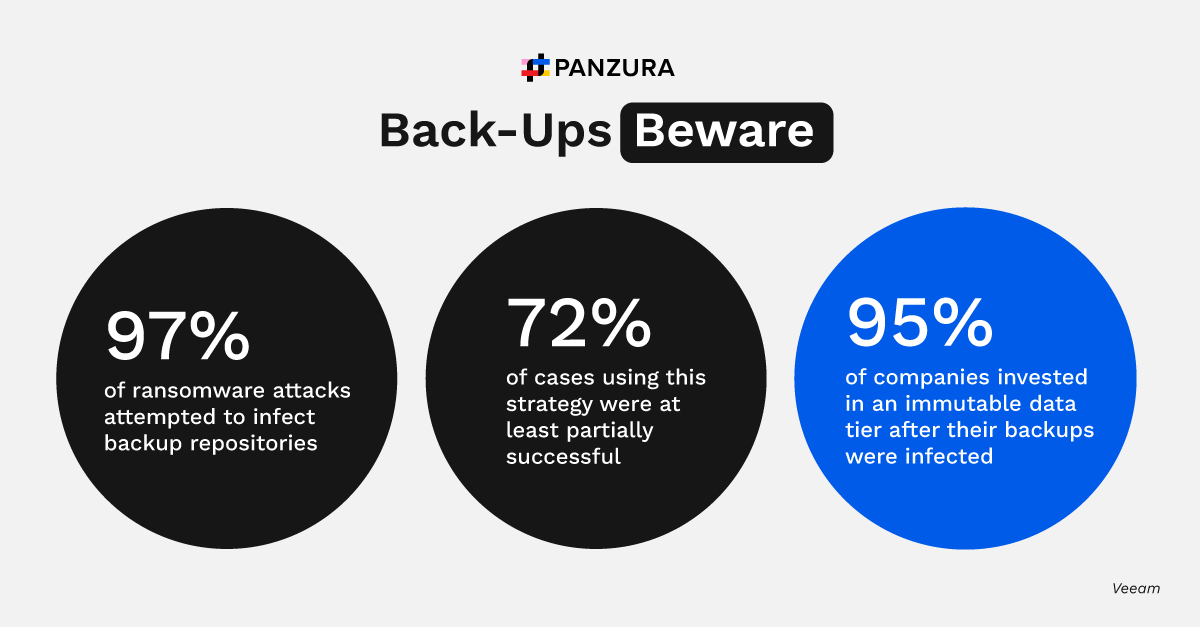
Sometimes, even a backup plan isn’t enough. A plan will help to some extent, but ransomware attackers are a step ahead. Often, they already know that you have a backup in place and plan to infect that, too.
Resilience in the Face of Ransomware
Panzura prevents companies from losing valuable data. Panzura CloudFS makes cloud object storage immutable, and thus, impervious to ransomware. Any edits made by attackers don’t destructively replace the file data, but instead create new blocks. Your actual files can never be irreversibly encrypted because they can never be overwritten.
With Panzura, infected doesn’t mean affected.
Stay a step ahead of ransomware attacks. Get the latest data on the real-world impact of ransomware.
Download Infographic
Download the Latest Data on Attacks & Their Impact
Stay a step ahead of ransomware attacks.
Download Infographic